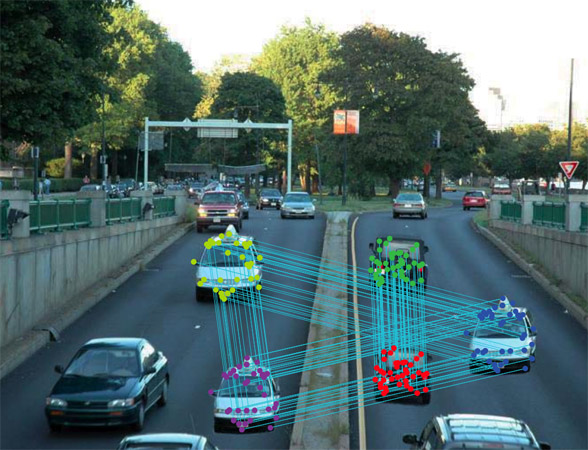
In many application scenarios digital images play a basic role and often it is important to assess if their content is realistic or has been manipulated to mislead watcher’s opinion. Image forensics tools provide answers to similar questions. We are working on a novel method that focuses in particular on the problem of detecting if a feigned image has been created by cloning an area of the image onto another zone to make a duplication or to cancel something awkward.
The proposed approach is based on SIFT features and allows both to understand if a copy-move attack has occurred and which are the image points involved, and, furthermore, to recover which has been the geometric transformation happened to perform cloning, by computing the transformation parameters. In fact when a copy-move attack takes place, usually an affine transformation is applied to the image patch selected to fit in a specified position according to that context. Our experimental results confirm that the technique is able to precisely individuate the altered area and, in addition, to estimate the geometric transformation parameters with high reliability. The method also deals with multiple cloning.
Demo Video:
Related Publication:
- Amerini, I., L. Ballan, R. Caldelli, A. Del Bimbo, L. Del Tongo, and G. Serra, “Copy-Move Forgery Detection and Localization by Means of Robust Clustering with J-Linkage“, Signal Processing: Image Communication, vol. 28, issue 6, 2013.
- Amerini, I., L. Ballan, R. Caldelli, A. Del Bimbo, and G. Serra, “A SIFT-based forensic method for copy-move attack detection and transformation recovery“, IEEE Transactions on Information Forensics and Security, vol. 6, pp. 1099–1110, September, 2011.
- Caldelli, R., I. Amerini, L. Ballan, G. Serra, M. Barni, and A.. Costanzo, “On the effectiveness of local warping against SIFT-based copy-move detection“, Proc. of International Symposium on Communications, Control and Signal Processing (ISCCSP), Roma, Italy, May, 2012.
- Amerini, I., L. Ballan, R. Caldelli, A. Del Bimbo, L. Del Tongo, and G. Serra, “An image forensics tool for copy-move detection and localization“, Proc. of IEEE International Conference on Multimedia & Expo (ICME), Barcelona, Spain, July, 2011.
- Amerini, I., L. Ballan, R. Caldelli, A. Del Bimbo, L. Del Tongo, and G. Serra, “An image forensics tool for copy-move detection and localization“, Proc. of IEEE International Conference on Multimedia & Expo (ICME), Barcelona, Spain, July, 2011.
Code:
- MICC-F220: this dataset is composed by 220 images; 110 are tampered and 110 originals.
- MICC-F2000: this dataset is composed by 2000 images; 700 are tampered and 1300 originals.
- MICC-F8multi: 8 tampered images with realistic multiple cloning.
- MICC-F600: this dataset is composed by 600 high resolution images containing realistic and challenging copy-move attacks; 160 are tampered images and 440 are originals. This file is password protected so send me an e-mail requesting the password if you are interested.